Fictional portrayals of computer programming, hacking, and cybersecurity are often exaggerated – and far too often, they come across as totally inaccurate to experts and enthusiasts.
How many times have you watched a hacking scene in a movie or television show, and thought things did not look quite right? Have you ever thought that a video game’s portrayal of cybersecurity is completely off the mark?
It takes more than a few lines of code to test a server, there is rarely a single large red button, and computer users do need the mouse – but that is not what most fictional portrayals would have you think penetration testing or programming really looks like.
Realistic Hacking Games
For a visual overview of some of these titles, you might find this video informative:
Realistic hacking games offer players an immersive experience by simulating authentic cybersecurity practices and challenges. “Hacknet” stands out by providing a Unix-like operating system interface, allowing players to execute real hacking commands and navigate through a simulated file system, closely mirroring real-world hacking scenarios. Similarly, “Exapunks” immerses players in a cyberpunk setting where they write code to manipulate in-game systems, offering a deep dive into programming logic and problem-solving. Another notable title, “Quadrilateral Cowboy,” equips players with a “top-of-the-line hacking deck” to infiltrate secure systems, emphasizing strategic planning and execution. These games not only entertain but also educate players about the intricacies of hacking and cybersecurity. en.wikipedia.org+3thecyberexpress.com+3en.wikipedia.org+3en.wikipedia.orgen.wikipedia.org+1pcgamesn.com+1en.wikipedia.org+1pcgamesn.com+1
Top Five Amazon Books on Cybersecurity and Hacking:
1. “The Art of Invisibility” by Kevin Mitnick
o Description: Authored by renowned hacker Kevin Mitnick, this book delves into the intricacies of online privacy and how individuals can protect themselves in the digital age. To read the reviews click HERE.
2. “Hacking: The Art of Exploitation” by Jon Erickson
o Description: This book provides a comprehensive look into the world of hacking, covering topics from programming to network communications, and offers hands-on examples. To read the reviews click HERE.
3. “Ghost in the Wires: My Adventures as the World’s Most Wanted Hacker” by Kevin Mitnick
o Description: An autobiographical account of Mitnick’s experiences as a hacker, detailing his exploits and eventual capture by the authorities. To read the reviews click HERE.
4. “Metasploit: The Penetration Tester’s Guide” by David Kennedy, Jim O’Gorman, Devon Kearns, and Mati Aharoni
o Description: A guide to using the Metasploit Framework, this book is essential for those interested in penetration testing and cybersecurity. To read the reviews click HERE.
5. “The Web Application Hacker’s Handbook” by Dafydd Stuttard and Marcus Pinto
o Description: This handbook offers deep insights into web application security, teaching readers how to identify and exploit vulnerabilities. To read the reviews click HERE.
Top Five Gaming Equipment Recommendations Available On Amazon:
Based on current information and available products, here are five top gaming equipment recommendations available on Amazon:
1. “Logitech G Pro X Superlight 2 gaming mouse”}】 Logitech G Pro X Superlight 2 Wireless Gaming Mouse
o This ultra-lightweight mouse features Logitech’s Hero 2 sensor with up to 32,000 DPI, a 4kHz polling rate, and offers up to 95 hours of battery life. It’s designed for both work and gaming, providing precision and comfort. To read the reviews click HERE.
2. “Xbox Wireless Controller
o Known for its ergonomic design and versatility, this controller supports both Bluetooth and USB-C connectivity, making it compatible with Xbox consoles, PCs, and mobile devices. It features a battery bay that accommodates standard AA batteries or rechargeable packs for extended playtime. To read the reviews click HERE.
3 “BENGOO G9000 Stereo Gaming Headset”
o BENGOO G9000 Stereo Gaming Headset
This headset offers noise-canceling over-ear headphones with a mic, LED lights, bass surround sound, and soft memory earmuffs, enhancing the gaming experience across multiple platforms. To read the reviews click HERE.
4. “NUBWO G06 Wireless Gaming Headset”}】 NUBWO G06 Wireless Gaming Headset
o Featuring low latency audio, up to 100 hours of playtime, and 50mm drivers, this headset is compatible with PS5, PS4, and PC, providing immersive sound quality for gamers.To read the reviews click HERE.
5. Redragon K585 DITI One-Handed RGB Mechanical Gaming Keyboard
o This keyboard offers 42 keys with an upgraded hot-swappable socket, 7 onboard macro keys, and a detachable wrist rest, catering to professional gaming needs. To read the reviews click HERE.
More accurate cybersecurity and hacking portrayals in video games exist!
All programmers love the potential that a good puzzle holds. That is why many people with an interest in cybersecurity naturally take well to gaming.
Do you feel like a challenge – but with the benefit of accuracy?
Here are the most accurate video games about cybersecurity & hacking.
System Shock 2

System Shock 2 was first released in 1999 as a futuristic survival-horror first-person shooter with added role-playing aspects.
If you are a fan of any high-octane action games (or creepy survival games), you must play System Shock 2 at least once.
What puts it on this list of great cybersecurity and hacking games is the aspect of augmenting the player or altering the environment. It is more visual than command-line, but it is still accurate (and very, very complimentary to the rest of the game).
Enter the Matrix

Enter the Matrix was released for PC and various console platforms in 2003.
The game takes the player into the Matrix universe, with a third-person shooter perspective throughout most of the gameplay. Combat and the ability to slow time down for fighting sequences (or dodging bullets) added whole new elements that have been widely copied in other games.
Where does the hacking come in?
Players can “hack” into the Matrix through an elaborate command-line interface at any point during gameplay. Easter eggs from the series and upgrades for the player are available when this is done right.
Uplink

Uplink was released in 2001 and is one of the few games that exclusively functions through a visual user-interface which the player uses to access various game features.
It is a fictional hacking simulation which puts the player into the system of a futuristic, anti-corporation hacker-for-hire. Jobs can be searched for on classified boards, and the player has their choice of which jobs they want to accept.
In-game currency is earned and used to purchase software or system upgrades to improve the ability or speed of your virtual hacks.
Points for accuracy, and the extreme elaborate nature of the game in which the player is free to do as they like to earn their living.
Hacker

Hacker is a classic title released in 1985, when it seems like most of popular culture was still trying to figure out what the word “hacking” means.
It is like Uplink in its anti-establishment storyline, though relied far more on the command-line aspects of hacking to make the game. It plays well, and its complexity has literally stood the test of time.
If you were to play it today, it is still an excellent game – and a better portrayal of command-line programming in fiction than most modernized stories would manage.
Hacker II: The Doomsday Papers
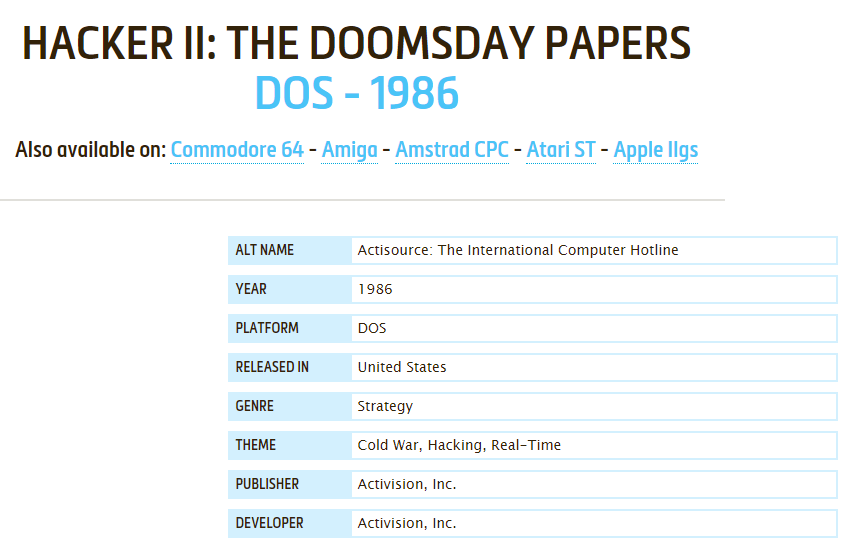
The almost immediate popularity of the first Hacker title spawned a sequel the next year with Hacker II: The Doomsday Papers.
For the most part, the storyline builds on the one laid by the first – and the command-line programming aspect is kept.
Like the first game in the series, it is almost more accurate than many fictional cybersecurity portrayals that you would see today. The good news is that the game is perfectly understandable even if you did not play the first one.
Play it, and you surely will not be disappointed.
Hackmud
Hackmud is a modern mixture of a hacking simulator and an RPG.
The game relies heavily on a command-line interface, with an added cyberpunk theme and storyline that is written well enough to make players forget about “fancier” game visuals. Hackmud is elaborate and meant to be played in real-time.
So far, it is one of the most accurate hacking simulation games out there and has been praised by its accuracy since its release.
Have you tried Hackmud yet?
If not, you should.
Street Hacker
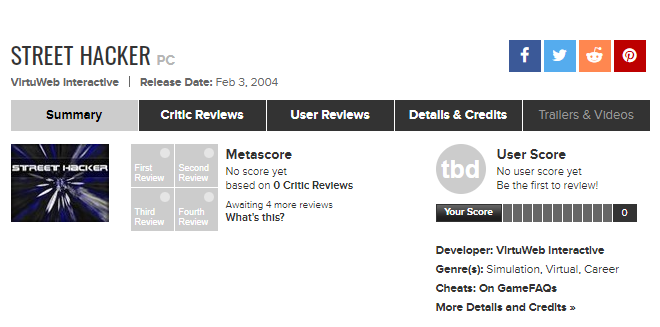
Street Hacker was released in 2004, and almost immediately praised by critics for its accuracy in portraying real cybersecurity threats weaved into a fictional storyline.
Players assume the role of a “street hacker” in much the same style as other hacking games.
Why this game gets mentioned is the accuracy in portraying command-line programming on Linux systems.
In gaming, that is a rare thing for developers to get right.
Street Hacker hits the spot for anyone interested in game development, cybersecurity, or programming.
HEX Hacking Simulator

HEX Hacking Simulator is described well enough by its name.
Created by Solis Studios, it is another game which draws on the hacker-for-hire idea – but this time, the game incorporates malicious cybersecurity terms from real life (like worms versus horses) and explains them in-game.
For accuracy on which cybersecurity nasties do what in practice, this title gets it right.
Students of tech, pay attention.
tryhackme
TryHackMe is partially a game, but partially a real-life server simulation – with a website that encourages penetration testing with programming and exploitation challenges for users.
“Hacktivites” and other challenges like “King of the Hill” let users test their programming and penetration skills in real-time, against real puzzles and programs built for the purpose.
It is a popular idea, with more than 400, 000 users involved in this real-life cybersecurity simulation site.
Could you learn how penetration testing really works?
TryHackMe can teach you.
This is a guest post contribution from Alex J Coyne